The errors that you may encounter systematically on internet platforms are called “Bug Bounty”. You have the right to report any vulnerabilities you encounter on the EgeMoney platform. To report a bug:
The errors that you may encounter systematically on internet platforms are called “Bug Bounty”. You have the right to report any vulnerabilities you encounter on the EgeMoney platform. To report a bug:
- Firstly, click on the “Bug Bounty” heading at the bottom menu of our website.
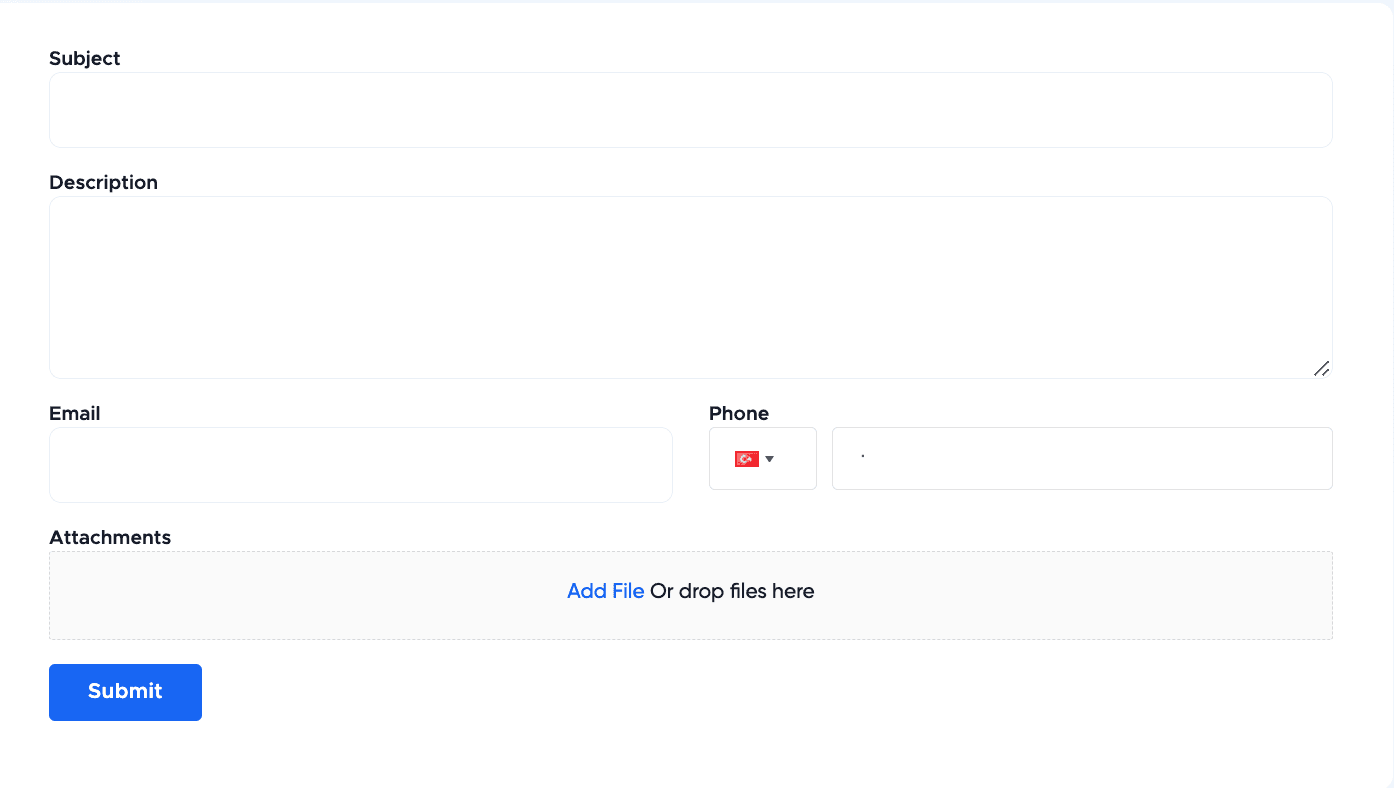
- On the page that appears, basically you will see a panel of spaces with the information you need to enter.

- In this panel, you should enter your findings about the error you detected. First of all, write the subject you want to report in the space at the top.
- Secondly, explain the topic more broadly in the next space. Make sure that the error you detect is understandable.
- Enter your e-mail and mobile phone number in the spaces on the 3rd line.
- Finally, if there is a file you want to add, you can use the attach option at the bottom.
What should I pay attention to when reporting an error?
- Only reports transmitted from the egemoney.com/bug_bounty address are evaluated. Reports transmitted using different channels are not considered.
- Only posts that are described in detailed and repeatable steps are responded to.
- If a vulnerability you submit triggers another one, please submit both vulnerabilities separately. Only one vulnerability per submission.
- Vulnerabilities or findings that are outside the scope (see out of scope section at the bottom) will not be assessed.
- In cases where the same vulnerability is submitted by two or more people, only the first person who identified it will be rewarded and listed in our Hall of Fame.
- All submissions will be responded to within 3 days. The more important errors/bugs will be responded to more quickly.
- Sending your findings with a fake email address and credentials is forbidden. Submission from these accounts will not be assessed.
- The person who has the vulnerabilities should be the one submitting them. Don’t submit security flaws on other people’s behalf.
- The right to share the submitted vulnerabilities with the public, third-party partners, or employees is reserved by EgeMoney.
- When you make a submission, you accept the terms and conditions of our program.
- The privacy of other users should not be neglected.
- You should avoid actions that will disrupt our services or destroy our data.
- Do not share the security vulnerabilities you have detected on other platforms.
- Don’t submit the same vulnerability multiple times.
What topics are not included in Bug Bounty?
Topics remain within the scope of EgeMoney’s Bug Bounty Program and rewards:
- Theoretical vulnerabilities without scans, reports from automated tools, or actual proof of concept.
- Vulnerabilities that are unconnected to EgeMoney’s platforms.
- Vulnerabilities to assets that do not belong to EgeMoney.
- Any kind of physical attack, a man-in-the-middle attack (MITM), spamming, phishing, smishing, or social engineering attack.
- Any vulnerability that is already known to us. Features that are in the development stage. Vulnerabilities that are already submitted to us by another researcher.
- Vulnerabilities that aren’t reproducible.
- Any vulnerability related to missing security headers, content security configuration (CSP), or CSRF that does not lead to any direct exploitation.
EgeMoney Bug Bounty Program Reward
- The base reward in our EgeMoney Bug Bounty Program is 2 USDT. Rewards will vary on the severity and impact of the vulnerability submitted. In addition, you will always receive over 2 USDT.
- Not all findings will be receiving a monetary reward. Findings that have no serious impact will only be listed in our Hall of Fame, and findings that have a more serious impact may receive a reward of more than the minimum amount.
- There is a single reward for each vulnerability, so only the first person to submit a security flaw will receive a reward.
For more information about the Bug Bounty Program, you can review the relevant page.
Merhaba! İçerik ekibimiz, çeşitli uzmanlık alanlarına sahip deneyimli yazarlardan oluşmaktadır. Bizi takip ederek en güncel bilgilere ulaşın.